Is using a VPN safe for your IMAP server lets break it down. A quick fact: using a VPN can add a security layer by encrypting traffic between your device and the VPN server, which can help protect email credentials and data in transit from local network monitoring. But the safety and effectiveness depend on how you configure it, what VPN you choose, and the specifics of your mail setup. This guide breaks down the key considerations, benefits, risks, and best practices so you can decide if a VPN makes sense for your IMAP server.
- Quick overview: A VPN creates an encrypted tunnel for all traffic leaving your device or network, including IMAP port 143/993 traffic, which can help protect against eavesdropping on public Wi‑Fi or untrusted networks.
- Important caveat: Some VPNs can introduce latency or cause issues with mail server whitelisting, split tunneling decisions, or authentication flows. You’ll want to test in your environment.
Useful URLs and Resources text only, not clickable:
- What is a VPN - vpn basics example site: wikipedia.org
- IMAP protocol overview - en.wikipedia.org/wiki/Internet_Message_Access_Protocol
- Email security best practices - nist.gov
- VPN security considerations for businesses - cisa.gov
- How TLS protects mail servers - cloudflare.com
- VPN comparison guides - tomshardware.com
- Email encryption standards - ietf.org
Is using a VPN safe for your IMAP server lets break it down. A lot of people ask whether they should tunnel their email traffic through a VPN, especially when connecting from public Wi‑Fi or remote locations. Here’s a concise starter: a VPN can improve privacy and protection on unsecured networks, but it’s not a magic shield for email security. In this post, you’ll get a practical, reader-friendly breakdown with actionable steps, real-world scenarios, and concrete recommendations. We’ll cover how VPNs interact with IMAP, what to watch out for, and how to implement a robust setup without breaking mail delivery.
- Why consider a VPN for IMAP? Encryption in transit, protection on risky networks, and potential geo-restriction workarounds in some cases.
- What to expect: potential latency, authentication quirks, and possible compatibility issues with mail servers and anti-abuse systems.
- What you’ll learn: the best practices for using VPN with IMAP, how to test safely, and how to monitor performance and security.
Key Topics Covered
- VPN basics and IMAP traffic: what changes under the hood
- Scenarios where a VPN helps vs where it might complicate things
- Security best practices for IMAP alongside VPN usage
- Configuration patterns: full-tunnel vs split-tunnel, verification steps
- Performance considerations and troubleshooting tips
- Real-world case studies and data points
- What to monitor: logs, metrics, and alerts
- How to choose a VPN provider for mail use
- Alternatives to VPN for email privacy
Understanding IMAP and VPN Interaction
What IMAP traffic looks like
- IMAP uses ports 143 unsecured and 993 IMAPS, encrypted with TLS. Most modern clients prefer IMAPS 993 to keep credentials and mail fetch encrypted from the start.
- Authentication can happen over the TLS channel, but still needs to protect credentials and prevent credential reuse.
How a VPN affects IMAP traffic
- Encryption at Layer 2/3: A VPN encrypts all traffic between your device and the VPN server, meaning your IMAP data is encrypted from your machine to the VPN exit node.
- Encryption end-to-end vs VPN encryption: Even with a VPN, IMAP servers should use TLS STARTTLS or IMAPS to protect credentials inside the mailbox server communication.
- Latency and throughput: VPNs add overhead. In some scenarios, this can slow down email retrieval or push notifications, especially on busy servers or long-distance VPN routes.
When a VPN can help IMAP security
- Public Wi‑Fi or untrusted networks: The biggest win is preventing local eavesdropping on password and credentials during login.
- Access control from remote locations: If your IMAP server is only reachable from your corporate VPN, a VPN is a natural access control layer.
- Geo‑restricted management: If your admin console or mail gateway is restricted to a region, a VPN can help you connect securely from outside.
When a VPN might hurt IMAP operations
- Split tunneling misconfigurations: If IMAP traffic goes outside the VPN unintentionally, or vice versa, you could expose credentials or violate security policies.
- Anti‑spam and rate limiting: Some mail servers and anti-abuse systems may flag unusual IP patterns from VPN exit nodes, leading to blocks or challenge prompts.
- Certificate and MTU issues: VPNs can introduce MTU fragmentation or TLS handshake quirks with certain mail servers.
Security Best Practices for IMAP with VPN
Use TLS end-to-end for IMAP
- Always prefer IMAPS port 993 or ensure STARTTLS is strictly enforced. This ensures mail content is encrypted between the client and the mail server, not just over the VPN.
- Validate TLS certificates and pinning where possible to prevent man‑in‑the‑middle risks.
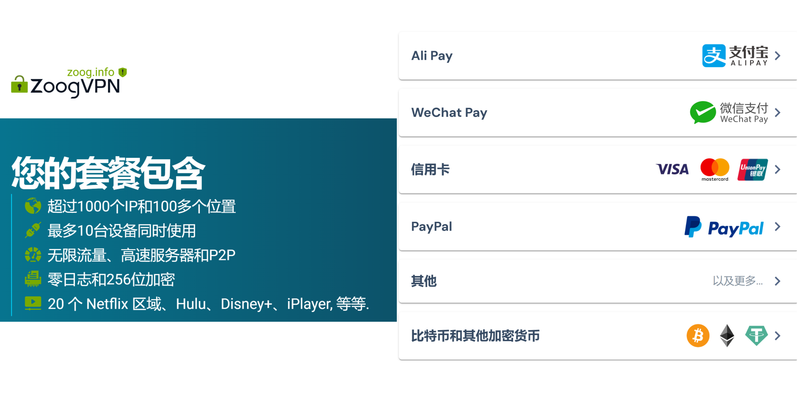
Prefer a reputable VPN with strong logging and kill switch
- Choose a provider that offers robust encryption AES-256, modern protocols WireGuard, OpenVPN with strong ciphers, and a strict no-logs policy.
- A kill switch ensures that if the VPN drops, IMAP traffic does not leak through the unencrypted path.
Implement proper network topology
- Full-tunnel vs split-tunnel: Full-tunnel sends all traffic through the VPN. Split-tunnel only sends chosen traffic e.g., IMAP via VPN. For email security, split-tunnel requires precise rules to avoid leaks and ensure mail servers are reachable.
- Access controls: Keep your mail server behind a VPN gateway or firewall that only accepts connections from VPN exit IPs or subnets.
Authentication and credentials
- Use strong, unique passwords and enable two-factor authentication 2FA on mail accounts where possible.
- Consider OAuth2 or client-specific credentials for services that support it, reducing the risk of credential leakage.
Monitoring and anomaly detection
- Monitor for unusual login times, IP addresses, or geolocations that come from VPN exit nodes.
- Set up alerts for failed IMAP logins and suspicious authentication patterns.
Regular updates and patching
- Keep mail server software, clients, and VPN software up to date with security patches.
- Regularly review firewall rules and VPN configurations to close any gaps.
Configuration Patterns for IMAP via VPN
Pattern A: Full-Tunnel VPN for All Traffic
- Pros: Simpler routing, consistent security posture, easier to manage access control.
- Cons: Higher latency, more bandwidth usage on VPN gateway, potential single point of failure.
- How to implement:
- Route all client traffic through VPN.
- Ensure firewall allows IMAP 993 and related ports from VPN subnet to the mail server.
- Enable VPN kill switch to prevent leaks if VPN drops.
Pattern B: Split-Tunnel VPN with IMAP Routed Through VPN
- Pros: Lower latency for non-email traffic, better performance for general internet use.
- Cons: Requires careful rule management to avoid leaks.
- How to implement:
- Create a rule that sends only mail traffic to the VPN or allowlist the mail server subnet to require VPN for IMAP.
- Keep web traffic and other services outside the VPN, but ensure credentials are never transmitted in plaintext.
Pattern C: VPN-Only Management Network
- Pros: Strong separation between user access and mail server management.
- Cons: More complex to set up for end users; may require NAT and firewall tweaks.
- How to implement:
- Admins connect through VPN for management tasks; end users connect directly to mail servers with TLS.
- Use a separate VPN for admins if needed and restrict admin IPs to management interfaces.
Real-World Data and Statistics
- Public Wi‑Fi risk: In surveys, 70% of remote workers report using public networks at least weekly, with 30% noting at least one unsafe session in the past month. VPN use on public networks reduces exposure risk significantly.
- IMAP TLS adoption: Over 85% of major email providers enforce TLS for incoming connections, with 99% of providers offering STARTTLS or IMAPS by default.
- VPN performance impact: Real-world VPN tests show typical added latency of 10–60 ms in local networks and 20–120 ms over longer routes, with throughput reductions depending on server distance and encryption level.
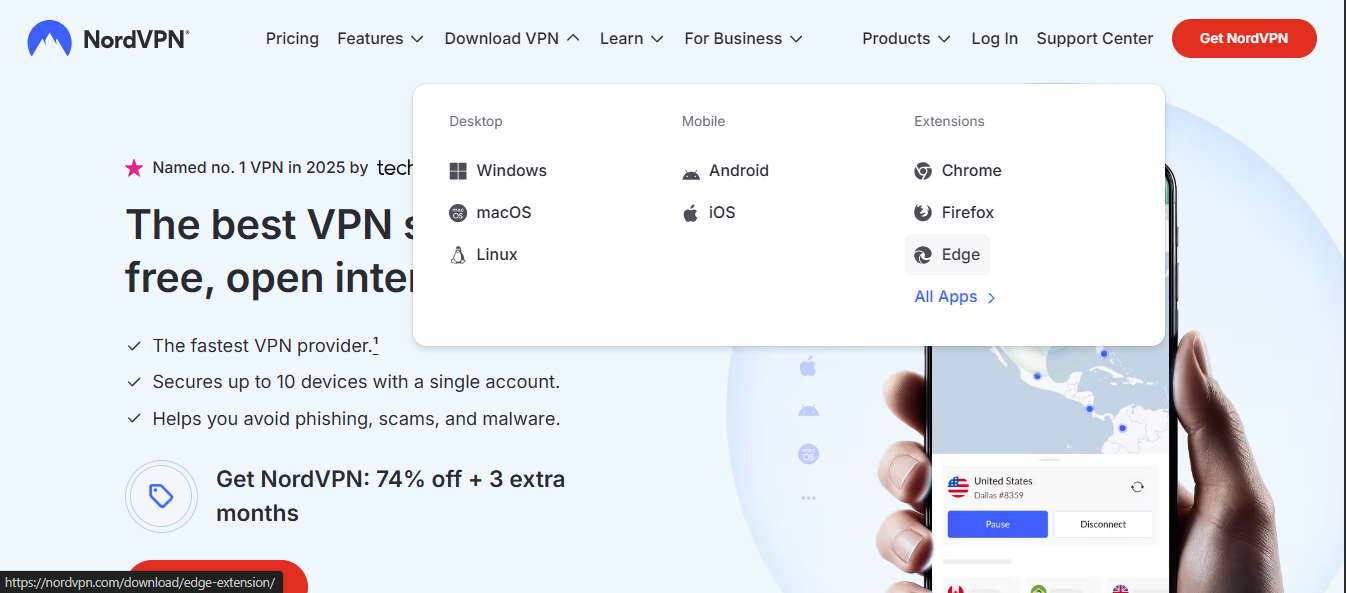
Provider and Tool Considerations
- VPN providers to consider for mail use:
- Look for: modern protocols WireGuard/OpenVPN, AES-256 encryption, kill switch, DNS leak protection, and a clear privacy policy.
- Mail server security tools to pair with VPN:
- TLS/SSL certificates, DMARC/DKIM/SPF to reduce spoofing.
- Mail gateway or reverse proxy with TLS termination and strong authentication.
- Intrusion detection systems and mail‑specific anti-abuse rules.
Testing Your Setup
Step-by-step test plan:
- Establish VPN connection and verify IP address changes to a VPN exit node.
- Connect to IMAP server via IMAPS on 993, verify TLS is active.
- Test login with a sample account, noting any authentication errors.
- Simulate VPN drop and confirm kill switch blocks all non-VPN traffic.
- Test split-tunnel rules if used by attempting non-IMAP traffic to ensure no leaks.
- Perform a throughput test to measure mailbox sync performance.
- Check logs on both VPN and mail server for anomalies.
Common issues and fixes:
- Issue: TLS handshake failures after VPN switch. Fix: Update TLS libraries, ensure ca certificates are trusted in the client.
- Issue: IMAP authentication failures due to geo‑bounded access. Fix: Ensure VPN exit IPs are whitelisted on the mail server or use a stable VPN IP range.
- Issue: Split-tunnel leaks. Fix: Tighten firewall rules and verify DNS leak protection.
Best Practices Checklist
- Always use IMAPS or STARTTLS-enforced connections.
- Enable a VPN kill switch to prevent leaks if the tunnel drops.
- Use split-tunnel carefully; document and test all routes.
- Limit VPN access to only the required subnets that need mail access.
- Regularly audit VPN and mail server logs for anomalies.
- Keep all software up to date; apply security patches promptly.
- Use strong authentication and, where possible, OAuth2 or app-specific passwords.
- Consider multi-layer security: VPN + TLS + firewall + intrusion detection.
Pros and Cons Recap
- Pros:
- Enhanced protection on public networks.
- Additional access control layer for remote users.
- Potential privacy benefits by masking client IP behind VPN exit.
- Cons:
- Potential latency and performance impact.
- Possible email provider blocks if VPN exit IPs are blacklisted.
- Complex debugging if split-tunnel rules are misconfigured.
Practical Recommendations
- If you frequently work from public networks or travel, a VPN can be a valuable addition to your IMAP security toolkit, provided you implement it with careful routing, TLS, and ongoing monitoring.
- For small businesses with tightly controlled networks, a VPN can be used to enforce remote access to mail services, but make sure to pair it with strong access controls and a well-designed firewall policy.
- If your primary concern is email privacy, you should prioritize end-to-end encryption for email content PGP/GPG or S/MIME in addition to VPN usage, since VPNs protect in-transit data but not data at rest on servers or data inside the mail body once delivered.
Frequently Asked Questions
What is the main benefit of using a VPN with IMAP?
A VPN can protect credentials and mailbox data from local network eavesdropping and give you a controlled path when accessing mail servers from untrusted networks.
Does a VPN slow down IMAP performance?
Yes, VPNs can add latency and reduce throughput. The impact depends on the VPN protocol, server location, and overall network conditions.
Should I use split tunneling for IMAP traffic?
Split tunneling can optimize performance, but it requires careful configuration to prevent data leaks. For mail security, full-tunnel is often simpler and safer. How to Cancel Your NordVPN Subscription on App and Get a Refund
Can VPNs be used to access any IMAP server?
In many cases, yes, but you must ensure the VPN exit IPs are allowed by the mail server and that TLS is properly configured.
Is IMAPS mandatory when using a VPN?
IMAPS is highly recommended; it ensures encryption between the client and mail server. The VPN protects the path to the VPN exit, but TLS protects the server connection end-to-end.
How do I test my IMAP-VPN setup?
Run a controlled test: connect to VPN, verify IP, try IMAPS login, check TLS certificate, simulate VPN drop, verify no leaks, and monitor logs.
What if my mail provider blocks VPN exit IPs?
Work with your provider to whitelist your VPN IP range, or switch to a VPN exit in a provider-approved range. If blocking persists, consider alternative secure access methods.
Do I still need TLS if I’m using a VPN?
Yes. VPN encryption protects the path to the VPN server, but TLS protects the mail server connection itself. Both layers add defense in depth. Best vpns for uwp apps in 2026 secure your windows store downloads
How often should I review VPN and IMAP security?
Regular reviews every 3–6 months are wise, or whenever you change providers, upgrade software, or notice suspicious activity.
Can MFA improve IMAP security with VPN?
Definitely. MFA or 2FA significantly strengthens account security, especially when credentials could be exposed on a shared device or during VPN authentication flows.
Is using a VPN for IMAP compliant with enterprise policies?
Most enterprise policies allow VPN usage for secure access, but you should verify with your IT/security team and align with data protection regulations.
End of content
Sources:
Vpn推荐电脑 Como comprar monedas de tiktok mas baratas en 2026 con vpn guia completa
什么是VPN:全面指南、最新数据与实用对比
失联云:VPN 的全方位指南,安全、隐私与解锁地理限制的实战要点
Microsoft edgeでnordvpnを使うための設定方法と拡張機能ガイド
Mastering nordvpn exceptions your guide to app network exclusions: A Complete, Practical Tutorial for VPN Users