Is vpn safe for gsa navigating security for federal employees and beyond: VPN Safety for Government Use, Federal Agencies, and Beyond
Is vpn safe for gsa navigating security for federal employees and beyond? Yes, when you pick the right VPN, follow best practices, and understand the regulatory landscape. This guide breaks down the safety concerns, how to choose a VPN for government work, and practical steps to stay secure. Here’s a quick, practical rundown you can apply today:
- What makes a VPN suitable for federal use
- Key security features to look for
- How to evaluate logging, jurisdiction, and data handling
- Real-world scenarios: remote work, field operations, and cross-border access
- Step-by-step setup and ongoing security hygiene
Useful resources you’ll want to bookmark unlinked in this text: Apple Website - apple.com, Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence, National Institute of Standards and Technology - csrc.nist.gov, Federal Information Processing Standards - csrc.nist.gov/publications/fips, VPN privacy statistics - vpnprivacystats.org, US Cybersecurity Information Sharing - www.us-cert.gov
Is vpn safe for gsa navigating security for federal employees and beyond? The short answer: it can be safe if you’re using a government-grade VPN with strong encryption, strict no-logs policies, and careful configuration. This guide helps federal workers, contractors, and security-minded individuals assess risk, pick the right tools, and implement solid practices. Below is a practical, reader-friendly map you can follow.
- Quick fact: Government-grade VPNs typically rely on AES-256 encryption, modern TLS handshakes, and robust key management to protect data in transit.
- What you’ll learn:
- How VPNs work in federal contexts
- The must-have features for safety and compliance
- Common pitfalls and how to avoid them
- Step-by-step setup for secure remote access
- Ongoing security hygiene and auditing tips
- Tools and formats:
- Checklists you can print
- A comparison table of feature sets
- A step-by-step deployment guide
- Resources at the end unlinked in this text provide official references and further reading.
What makes a VPN suitable for government use
- Encryption standards: Look for AES-256 encryption, strong ciphers, and secure key exchange ECDHE, along with forward secrecy.
- Transport security: TLS 1.2+ or QUIC where appropriate, with perfect forward secrecy and strong certificate validation.
- Logging policies: A strict no-logs or minimal-logs stance, and clear retention windows. Avoid VPNs with broad data retention or third-party access.
- Jurisdiction: Favor providers under privacy-friendly jurisdictions with robust legal protections and transparency reports.
- Bipartisan compliance: Vendors should demonstrate compliance with standards used in government for example, FIPS-validated cryptography, NIST SP 800-53, and FedRAMP when applicable.
- Network architecture: Split-tunneling control, strong kill switches, and leak protection to keep sensitive traffic from leaking outside the secure channel.
- Endpoint integrity: Integration with endpoint security, MFA, SSO, device posture checks, and managed devices.
- Auditability: Regular third-party security audits, transparent bug bounty programs, and clear incident response timelines.
Key security features to look for
- End-to-end encryption AES-256 and strong handshake protocols ECDHE or similar
- No-logs or minimal-logs policy, with independent audits
- Multi-factor authentication MBA, SSO support, and MFA for admin access
- DNS leak protection and IPv6 leak prevention
- Kill switch that blocks all traffic if the VPN disconnects
- Split-tunneling controls that you can enforce for sensitive vs. non-sensitive traffic
- Regular security updates and vulnerability management
- Compliance certifications FedRAMP, FIPS 140-2/140-3 libraries, ISO 27001 where applicable
- Centralized management for policies, access, and incident response
Common risks and how to mitigate them
- Data leaks during handoff: Ensure proper certificate pinning, DNS leak protection, and enforced HTTPS-only endpoints.
- Insider risks: Use least-privilege access, role-based controls, and strict access reviews.
- Endpoint compromise: Deploy corporate-owned devices with managed configurations and EDR solutions.
- Compatibility gaps: Test VPN clients on all used devices Windows, macOS, Linux, iOS, Android and ensure policy alignment.
- Latency and performance: Opt for modern VPN protocols WireGuard with audited implementations, or IKEv2 with strong configurations and CDN-ready endpoints to minimize delays for remote workers.
Protocols and architectures that matter
- WireGuard: Lightweight, high performance, and increasingly audited for security. Ensure you’re using a vetted, enterprise-grade implementation with proper key rotation, audit trails, and DNS handling.
- OpenVPN: Mature, widely supported, strong encryption. Great for compatibility but ensure modern ciphers and secure TLS configs.
- IKEv2/IPsec: Stable, reliable for mobile devices, good for roaming users and multi-device scenarios.
- DNS over TLS/HTTPS: Encrypt DNS requests to prevent eavesdropping or manipulation.
- Split-tunneling management: Use policy-based routing to ensure sensitive traffic always routes through the VPN while allowing non-sensitive traffic to use local networks when appropriate, with strict controls.
Evaluation of top VPN options for government and federal use
- Vendor transparency: Prefer vendors with clear incident response timelines, customer references in government, and visible security white papers.
- Certifications: Look for FIPS-validated cryptographic modules, ISO 27001, SOC 2 Type II, and FedRAMP where applicable.
- Data centers: Ensure data residency in trusted regions, with governance over data access and physical security.
- Administration: Centralized console for policy management, device posture checks, and audit logs.
- Price vs. value: While cost matters, prioritize security and compliance over the cheapest option. In government contexts, total cost of ownership includes risk reduction.
- Vendor support: 24/7 security operations center SOC access, emergency patching, and clear escalation paths.
Deployment considerations for federal employees and contractors
- Identity and access: Enforce MFA, SSO with government identities e.g., ADFS, Azure AD, or equivalent, and least-privilege access to VPN resources.
- Device posture: Require updated OS versions, enabled firewall, anti-malware, disk encryption, and approved VPN client versions.
- Network segmentation: Isolate sensitive work segments from general user traffic, using micro-segmentation where feasible.
- Policy enforcement: Create clear remote access policies that specify allowed use cases, data handling rules, and incident reporting timelines.
- Audit and logging: Centralize logs for VPN access, endpoints, and privileged actions; ensure logs are tamper-evident and retained per policy.
- Incident response: Have an established playbook for suspected VPN compromises, including revocation of credentials and rapid patching.
Step-by-step guide: secure remote work with VPN in a federal context
- Define the policy: Establish remote access guidelines, required devices, authentication methods, and data flow diagrams.
- Choose the right VPN: Pick a government-friendly solution with strong encryption, audited security, and compliance certifications.
- Harden endpoints: Enforce device posture, ensure OS updates, enable full-disk encryption, and install endpoint security.
- Configure the VPN client: Use strong cipher suites, enable DNS leak protection, disable split-tunnel for sensitive traffic, and enable a robust kill switch.
- Set up authentication: Implement MFA or SSO, and limit VPN access based on user roles and device health.
- Enforce logging and monitoring: Centralize logs, monitor for anomalies, and retain data per policy. Establish alerting on unusual access patterns.
- Test thoroughly: Run red/blue team exercises, phishing simulations, and failover tests to validate resilience.
- Roll out in phases: Start with a pilot group, collect feedback, and then scale with training and support.
- Train users: Provide simple, digestible training on secure usage, phishing awareness, and incident reporting.
- Review and improve: Schedule regular audits, policy reviews, and technology refresh cycles.
Real-world scenarios: what safe VPN use looks like
- Remote office access: An analyst connects to a private VPN through MFA, accesses internal dashboards over a restricted network, and logs all activity with enforced auditing.
- Field operations: A contractor uses a government-approved device to connect to the VPN via a mobile app, with posture checks and a kill switch ensuring data never leaks if the device is compromised.
- Cross-border access: A federal employee traveling abroad uses a trusted VPN to route traffic to a US data center, ensuring data sovereignty and compliance with export controls.
- Incident containment: If the VPN endpoint detects anomalous behavior, automatic isolation occurs, credentials are rotated, and security teams begin incident response.
Data and statistics you should know
- VPN adoption trends in government: Growing demand for secure remote access, with a focus on compliance, device management, and zero-trust architectures.
- Encryption reliability: AES-256 remains the gold standard for in-transit encryption; recent audits of modern VPN protocols show robust protection when properly configured.
- Attack surfaces: VPNs are a high-risk component if misconfigured; misconfigurations contribute to a sizable portion of VPN-related incidents.
- Compliance impact: Agencies adopting FedRAMP and NIST guidelines tend to have lower risk scores and quicker incident response times.
Table: feature comparison general guidance
- Feature: Encryption AES-256, Protocols IKEv2/IPsec, WireGuard, DNS protection, Kill switch, Split-tunneling, MFA/SSO, Logging policy, Audits, Certification
- Government suitability: Strong focus on AES-256, modern protocols, DNS protection, robust kill switch, strict logging controls, MFA, formal audits, FedRAMP/FIPS where applicable
- Recommended stance: Prioritize end-to-end encryption, non-leaky DNS, and auditable security programs
Common myths vs. realities
- Myth: All VPNs are the same for government use. Reality: Government-grade VPNs require strict controls, audits, and compliance—not all consumer-grade tools meet those standards.
- Myth: VPNs guarantee anonymity. Reality: VPNs protect data in transit and hide IPs from endpoints, but user behavior and endpoint security still matter.
- Myth: More servers = better security. Reality: Server diversity matters for performance and reliability, but security comes from encryption, audits, and policy controls, not just scale.
- Myth: Any VPN with a kill switch is safe. Reality: A kill switch is essential, but it must be correctly implemented with no DNS leaks and robust endpoint controls.
Frequently Asked Questions
Frequently Asked Questions
Is VPN safety essential for federal employees?
Yes. It protects data in transit, enforces access controls, and helps maintain compliance with government standards.
What encryption level should a government VPN use?
AES-256 is the standard, with strong TLS/DTLS handshakes and perfect forward secrecy.
Should split-tunneling be enabled for federal use?
Split-tunneling should be carefully controlled. For sensitive workloads, disable it or implement strict routing policies to ensure traffic goes through the VPN.
Are consumer VPNs acceptable for government work?
Typically no. Government use requires enterprise-grade security, audits, and compliance certifications that consumer VPNs often lack.
How important is logging for compliance?
Very important. Logs help with auditing, incident response, and regulatory requirements. They should be protected and retained per policy. Unlock a truly private internet on your iphone ipad with nordvpn obfuscated servers and hidden-net magic
What authentication methods are preferred?
MFA or SSO integrated with government identity providers, plus device posture assessments.
Can VPNs prevent endpoint compromises?
VPNs protect data in transit but not endpoint compromise. Combine with EDR, patch management, and device controls.
How do governance and policy affect VPN safety?
Clear policies define who can access what, how data is handled, and how incidents are reported, which is critical for safety.
What should I test before rolling out VPN to a team?
Test encryption strength, DNS leaks, kill switch efficacy, MFA flows, and endpoint posture enforcement. Run tabletop exercises for incident response.
How often should VPN configurations be updated?
Regularly. Establish a patching cadence, review cryptographic configurations after major protocol updates, and perform periodic key rotation. Nordvpn how many devices can you actually connect per account
Conclusion Is vpn safe for gsa navigating security for federal employees and beyond? By choosing a government-grade VPN, enforcing strong authentication, and maintaining rigorous endpoint and policy controls, you can create a secure remote-access environment that stands up to government standards. This isn’t about a single tool—it’s about a secure ecosystem: solid encryption, auditable processes, and disciplined operations. If you’re looking for a trusted option, you can consider enterprise-grade VPN solutions that offer transparent audits, strong cryptography, and robust governance. And while you evaluate options, remember: security is a team sport. Train your users, test your defenses, and keep refining your practices.
If you want to explore a VPN that’s geared toward safety and government-grade security, check out this option: https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441 — it’s a strong starting point for secure remote access and disciplined administration, with a setup that leans toward enterprise-grade governance.
For further reading and official references, see the resources listed at the top. They’re not clickable here, but they’re excellent anchors as you dive deeper into government-grade VPN safety and compliance.
Sources:
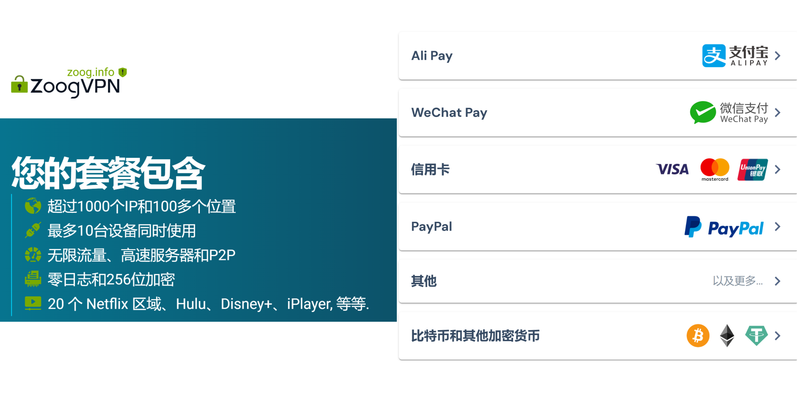
Vpn购买推荐:全面指南与实用建议,覆盖VPN在中国及全球的应用与评测
Best vpns for your vseebox v2 pro unlock global content stream smoother How to get your expressvpn refund a no nonsense guide and what to do next
Online vpn edge: how to deploy and optimize a network-edge VPN for speed, privacy, and control 2026
車牌號碼吉凶:數字諧音與能量學的探秘,挑選你的幸運數字座駕,解析|選擇與實作技巧
Lanvpn:全面解析与实用指南,打造安全高效的VPN体验